The Reason Why the Best Cyber Security Services in Dubai Are Vital for Every Service
The Reason Why the Best Cyber Security Services in Dubai Are Vital for Every Service
Blog Article
Discovering Just How Cyber Protection Functions to Guard Your Online Visibility
In today's digital landscape, shielding one's on the internet visibility has actually come to be significantly essential, with cyber hazards evolving at an alarming pace. Cyber security utilizes a diverse technique, integrating advanced innovations like firewall softwares, file encryption, and multi-factor verification to protect delicate info. How do these modern technologies work with each other to create a smooth shield versus cyber threats?
Comprehending Cyber Hazards
In the digital landscape, cyber risks stand for a formidable difficulty, needing a nuanced understanding of their nature and potential influence. These hazards include a broad variety of destructive activities coordinated by people, teams, and even nation-states, targeting sensitive information, disrupting procedures, or creating reputational damages. Understanding cyber threats begins with determining the different types they take, including malware, phishing, ransomware, and distributed denial-of-service (DDoS) strikes.
Malware, or malicious software, consists of infections, worms, and trojans that penetrate systems to cause or swipe information damage. Ransomware encrypts victims' data, requiring a ransom money for its release, positioning significant functional and economic dangers.
Recognizing the motivations behind these hazards is crucial. Cybercriminals usually look for financial gain, while hacktivists might seek ideological goals. State-sponsored assaulters might target critical framework for reconnaissance or destabilization purposes. By comprehensively recognizing the varied nature of cyber risks, companies can much better anticipate possible susceptabilities and strategically allocate sources to reinforce their defenses versus these ever-evolving dangers.
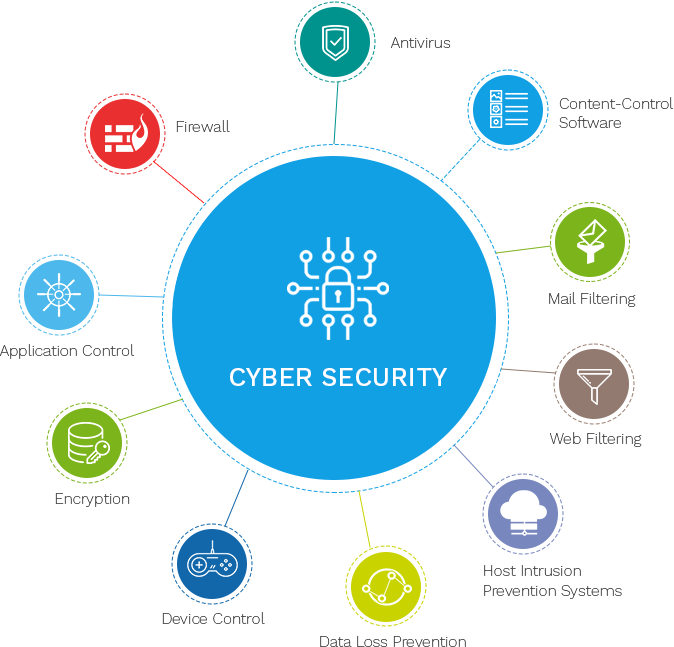
Key Cyber Protection Technologies
As organizations make every effort to protect their electronic assets, crucial cybersecurity technologies play a crucial function in strengthening defenses against cyber dangers. These technologies include a wide spectrum of tools and methods created to safeguard information honesty, confidentiality, and schedule. In today's electronic landscape, intrusion discovery systems (IDS) and breach prevention systems (IPS) are critical. IDS display network website traffic for questionable tasks, while IPS actively block prospective dangers, ensuring real-time security.
Additionally, anti-viruses and anti-malware options stay essential in determining and minimizing destructive software program. They use heuristic and signature-based strategies to identify unknown and known threats. Endpoint detection and response (EDR) systems further boost protection by supplying thorough presence into endpoint activities, enabling speedy case action.
Identity and access management (IAM) modern technologies make certain that just authorized customers get to vital resources, thereby lowering the danger of unauthorized information gain access to. Multifactor verification (MFA) includes an extra layer of safety, needing customers to offer multiple confirmation variables.
Additionally, safety information and occasion management (SIEM) systems aggregate and analyze protection information, supplying insights right into prospective susceptabilities and assisting in proactive hazard administration. These technologies collectively create a robust structure, empowering companies to keep a resistant cybersecurity position.
Role of Firewalls and Security
By managing outbound and inbound network web traffic, they protect against unapproved accessibility to systems and information. Firewall programs utilize predefined security rules to block or permit data packages, effectively shielding delicate details from cyber hazards.
Security, on the various other hand, changes legible information into an encoded format that can only be analyzed with a certain cryptographic secret. This process ensures that data continues to Visit This Link be safe and private during transmission or storage space. Even if intercepted, encrypted details is provided worthless to unapproved individuals without access to the decryption trick. Security is critical for shielding sensitive information such as economic information, personal recognition information, and proprietary business details.
With each other, firewall programs and file encryption provide a thorough protection mechanism. While firewalls take care of access and guard networks from unauthorized entry, security safeguards data integrity and discretion. Their integrated application is vital in mitigating risks and making sure the safety and find out here security of electronic possessions in an increasingly interconnected globe.

Significance of Multi-Factor Authentication
While firewall softwares and file encryption develop the backbone of cybersecurity, improving defenses even more needs the application of multi-factor verification (MFA) MFA includes an extra layer of protection by needing individuals to confirm their identity through two or even more various aspects prior to obtaining accessibility to sensitive information or systems. These factors commonly consist of something the individual knows (a password), something the customer has (a security token or smart device), and something the customer is (biometric verification such as a fingerprint or face recognition)
The importance of MFA in guarding on the internet presence is paramount in today's electronic landscape. With cyber risks becoming significantly sophisticated, counting exclusively on conventional password-based authentication leaves systems prone to breaches. MFA significantly lowers the danger of unapproved gain access to by making it significantly extra difficult for cybercriminals to compromise an account. Also if a password is stolen, the added confirmation steps act as a formidable barrier.

Behavioral Analytics in Cyber Safety And Security
Behavioral analytics stands for a crucial improvement in cybersecurity, using an advanced technique to danger detection and prevention. By examining patterns in user actions, this technique recognizes anomalies that may indicate potential cyber dangers.
This innovation is particularly efficient in identifying insider risks and zero-day assaults, which are commonly missed out on by traditional safety systems. Expert dangers, where people within a company misuse access opportunities, can be specifically damaging and tough to discover. Best Cyber Security Services in Dubai. Behavior analytics gives a layer of scrutiny that can capture subtle inconsistencies in behavior, such as uncommon accessibility patterns or information transfers, prior to they rise into considerable safety and security events
Additionally, the dynamic nature of behavior analytics enables it to adapt to advancing threats, giving continual protection as cyberattack approaches transform. As companies significantly count on electronic frameworks, incorporating behavior analytics right into cybersecurity strategies guarantees a resilient protection, safeguarding sensitive information and maintaining rely on electronic communications.
Final Thought
In verdict, the diverse strategy of cyber security, including technologies such as firewall programs, encryption, multi-factor verification, and behavior analytics, plays a vital duty in protecting on-line presence. By filtering website traffic, safeguarding data transmission, requiring several confirmation approaches, and checking individual activity for abnormalities, these technologies jointly deal with the complexities of contemporary cyber risks. This split defense not just safeguards economic and personal details but likewise guarantees continuous protection in an ever-evolving digital landscape.
As organizations aim to safeguard their digital properties, key cybersecurity technologies play a crucial duty in fortifying defenses versus cyber dangers. Firewall programs make use of predefined security policies to block or permit information packages, efficiently shielding delicate information from cyber dangers.This innovation is especially effective in identifying expert hazards and zero-day strikes, which are often missed by standard protection systems. By filtering system web traffic, protecting information transmission, calling for several verification techniques, and monitoring user activity for abnormalities, these modern technologies collectively deal with the intricacies of contemporary cyber threats.
Report this page